Recent posts by users in this instance
But first, let's see how this post fares. Here we go ...
[1] https://it-notes.dragas.net/2026/05/18/fedimeteo-haproxy-and-the-art-of-not-wasting-snac-threads/
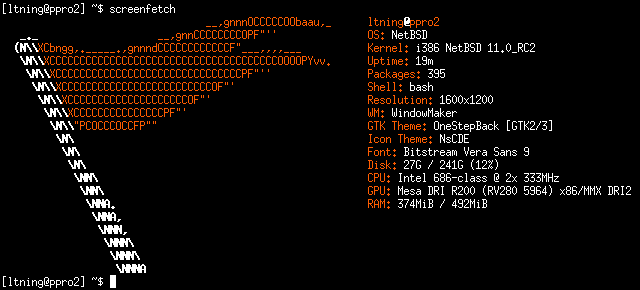
load averages: 7.70, 4.09, 2.66; up 0+00:41:42 21:55:40
74 processes: 3 runnable, 69 sleeping, 2 on CPU
CPU states: 28.4% user, 49.6% nice, 15.9% system, 4.6% interrupt, 1.3% idle
Memory: 241M Act, 120M Inact, 14M Wired, 57M Exec, 175M File, 5056K Free
Swap: 5120M Total, 45M Used, 5075M Free / Pools: 105M Used / Network: 67K In, 1035K OutPID USERNAME PRI NICE SIZE RES STATE TIME WCPU CPU COMMAND
686 root 17 10 59M 12M CPU/0 18:22 82.52% 82.52% snac
766 nginx 77 0 20M 8116K kqueue/0 0:51 31.15% 31.15% nginx
838 nginx 25 0 21M 8648K RUN/1 0:53 26.61% 26.61% nginx
734 root 76 0 72M 35M poll/0 5:19 22.22% 22.22% X
2528 root 73 10 29M 7124K wait/1 0:03 5.40% 4.00% pkg_add
1445 ltning 38 0 31M 12M RUN/1 0:57 3.76% 3.76% urxvt
3177 root 16 10 6144K 1228K RUN/1 0:00 13.17% 3.42% sh
3916 ltning 42 0 6748K 2456K CPU/1 0:01 2.45% 2.44% top
1332 ltning 85 0 7620K 2152K select/0 0:01 1.07% 1.07% xrootconsole
1103 ltning 85 0 42M 15M poll/1 0:52 0.93% 0.93% gkrellm
2342 root 77 10 29M 16M wait/0 1:09 0.68% 0.68% pkgin
1113 ltning 84 0 32M 11M select/1 0:50 0.59% 0.59% wmaker
0 root 127 0 0K 21M xcall/1 0:35 0.29% 0.29% [system]
I did receive some thinly veiled complaints about the (lack of) floor from others who use the space over the last few weeks.
Now I'll just sit here and look at it (and post about it) and see how long it can stay this way .. :P
(It was much worse before the "before" pic, but posting that would have required me to add a CW, I think..)
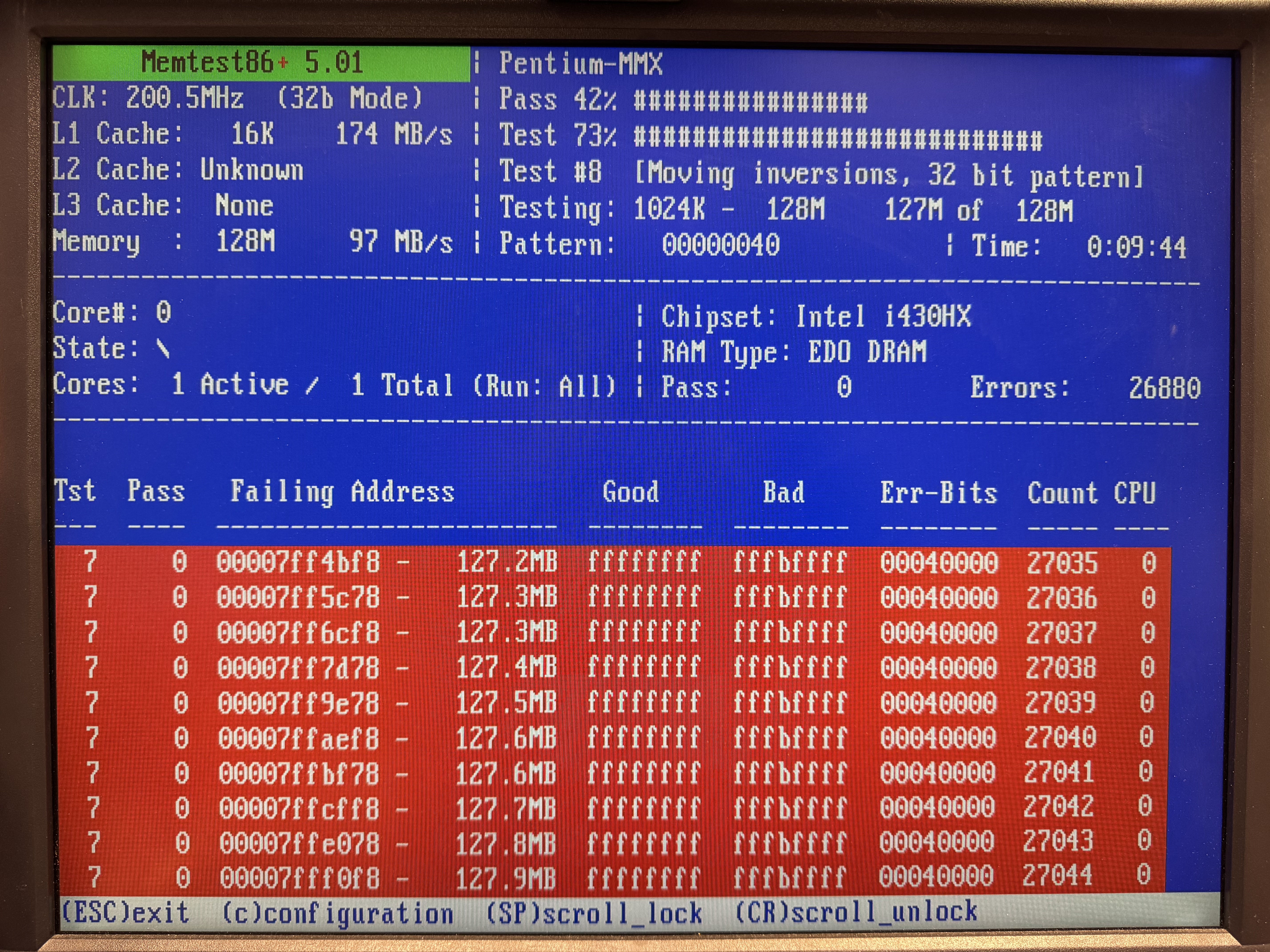
You may want to make sure you disable encrypted swap unless you have a ton of RAM. Someone seems to think that if you're on x86 you always have CPU to spare for encryption :D
Also, pkgin is fantastic and many (more than on OpenBSD) packages are built so they work on even an i486.
ISA performance can be "as good as it gets" on a PCI machine, and most BIOSes will allow you to configure it to a point that it can easily saturate the bus and even break stuff - just like in the good old days. Wait states and bus speed tuning being the most important things.
I also know that Tridents are not all garbage, but it is fair to say that the 9000-series (which is essentially a 8900C with some additional integration) isn't going to win any performance prizes no matter what machine you put it in. The 8900D on the other hand is quite impressive in DOS, keeping up with all but a small handful of much more expensive cards. It is, of course, useless for a GUI system since it has no acceleration functions, but for plain VGA it's pretty good.
All that said, I have not made any attempt at tuning for speed in these tests, and as I'm sure came across in my post - this is a highly un-scientific test that is only meant to gauge the relative difference between those cards (and with room for failure even at that). Fact of the matter, and what I wanted to confirm, is that the Matrox is unbelievably slow; I'm fairly sure the original VGA implementation with discrete chips (rather than a "VGA chip") would've performed better. Hell, even UniVBE warns me when configuring it that the card is unbearably slow in DOS, and doesn't even expose more than 1MB in VGA mode, so I should not expect much from it. Well, I guess I confirmed that, at least. :D
The reason is, of course, that the Matrox is made for GUI applications. And in those, compared to its peers, it absolutely shines according to reviews at the time. I'm looking forward to testing it in a GUI environment, and I'll surely post about that somewhere as well. And I'll use more period-correct hardware, I promise! :)
TL;DR: ISA Matrox cards are really, really slow in DOS.
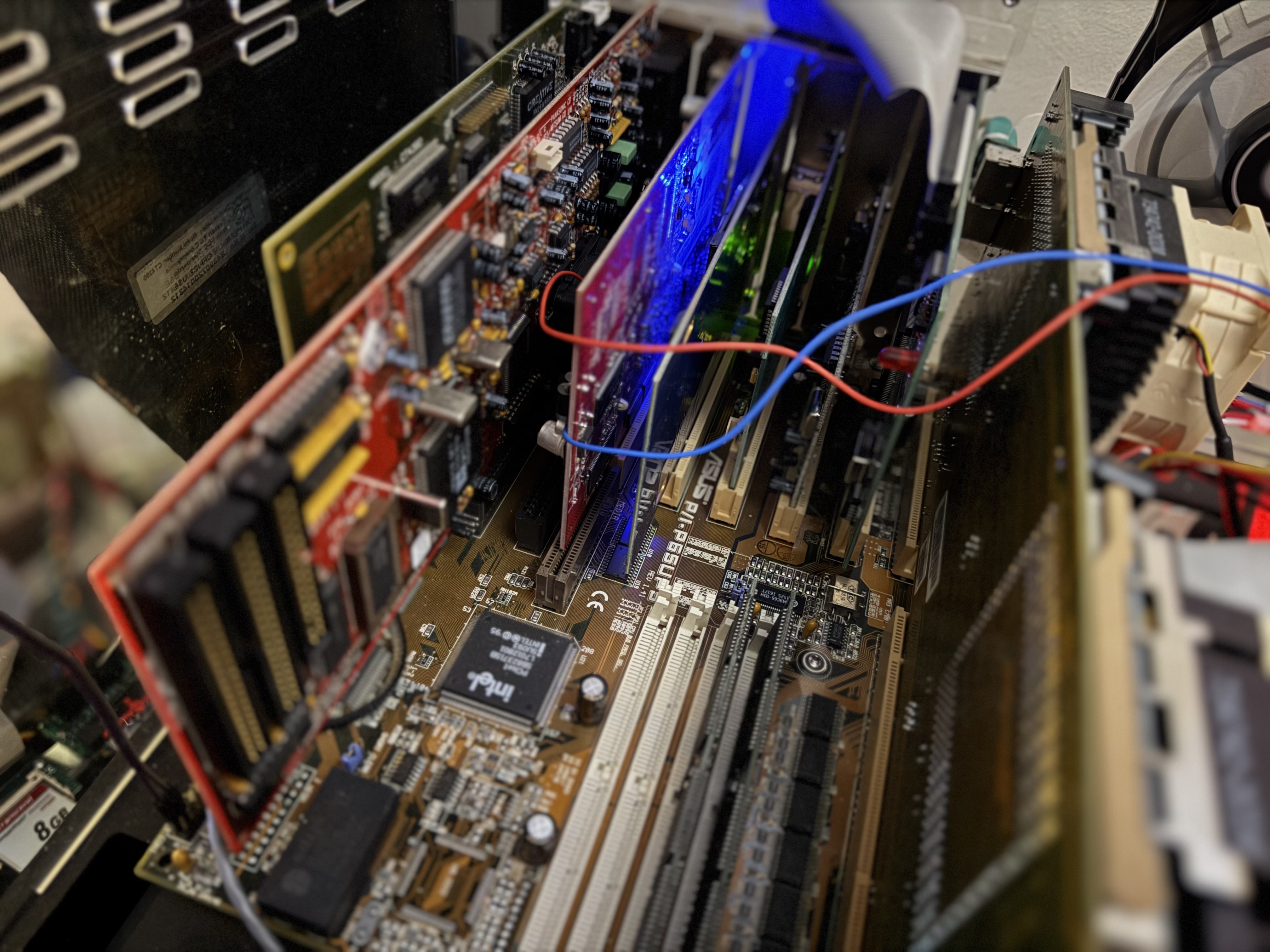
I recently built an original Pentium 60MHz system, built on an ECS motherboard. Around the same time I received a "mystery" VGA card: A Matrox MGA Impression ISA card. And since most of my builds are "open builds" and therefore easily accessible, that machine got the pleasure of becoming the test bench for the Matrox.
As already revealed, the Matrox performs atrociously bad. So bad, in fact, that I had to test a couple other ISA cards to make sure it wasn't a system issue. I used my go-to benchmarking tool #3DBench from Phil's DOS Benchmark Pack. I really don't want to experience Doom with this card..
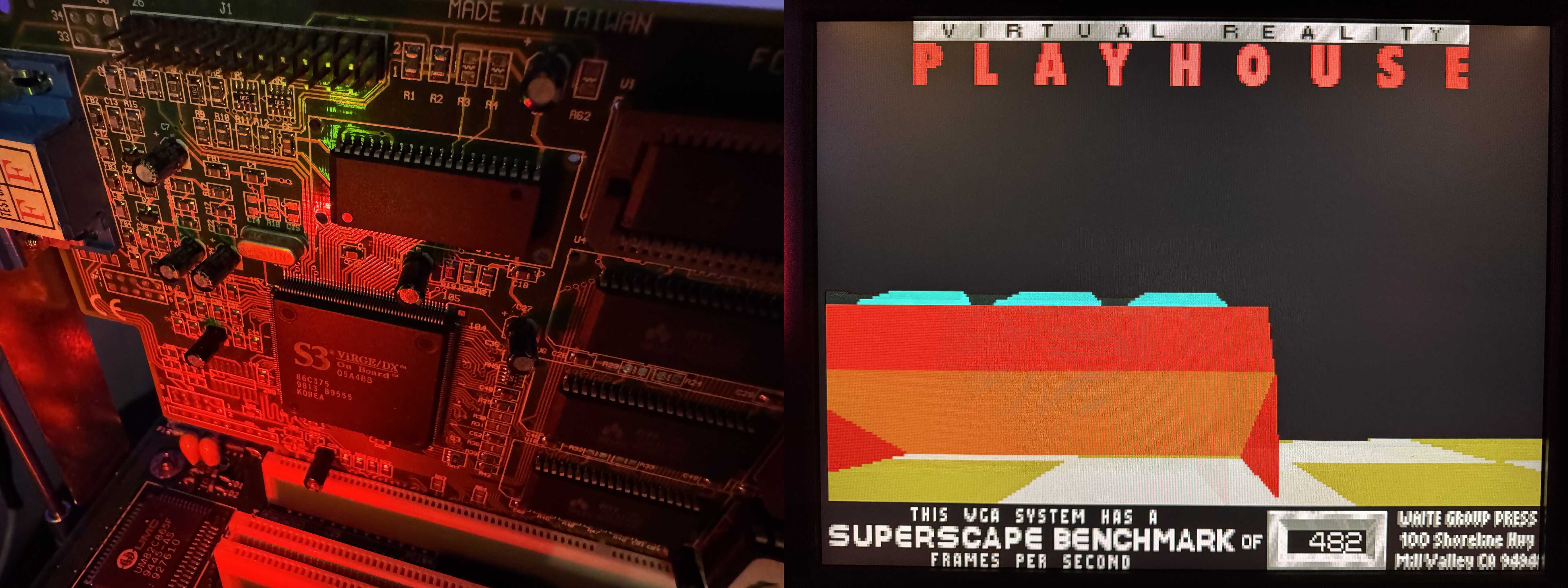
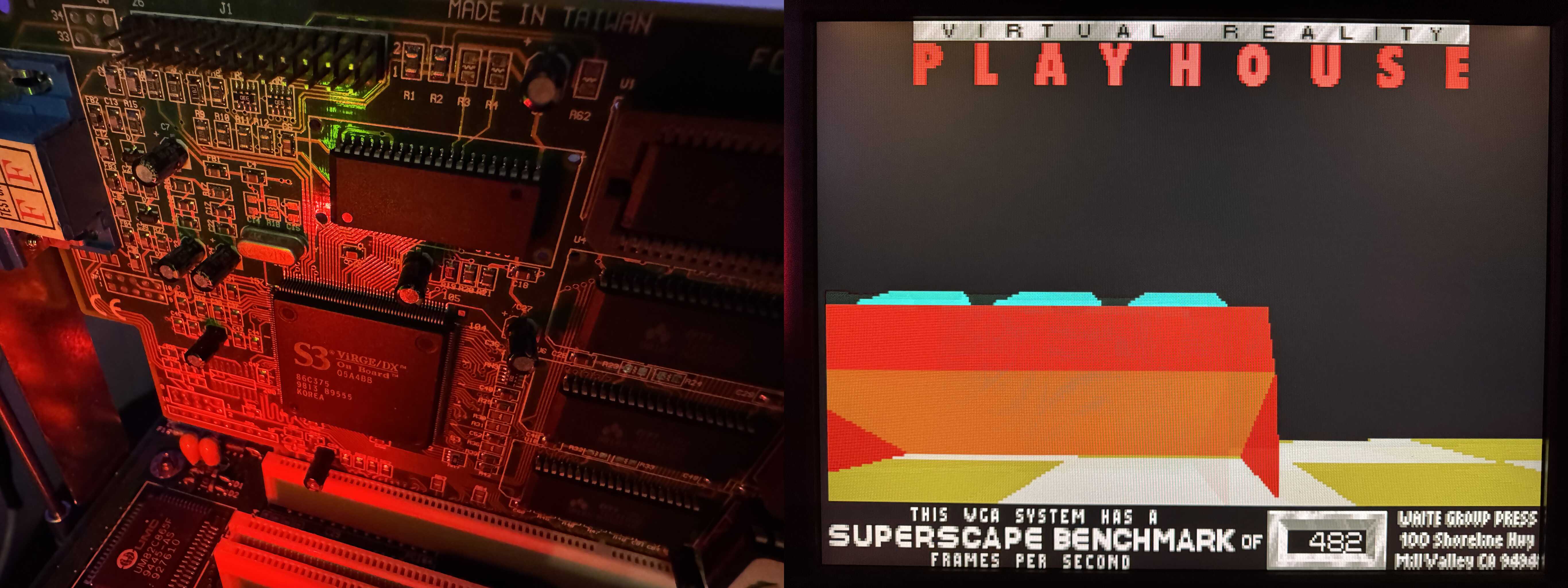
And without further ado, the contestants and their results in this spur-of-the-moment benchmark run:
- Baseline: A 32-bit PCI S3 Virge/DX based card with 4MB RAM: A perfectly workable 48.2
- The low-end Trident TVGA9000C with 512KB RAM (this is a real garbage card): A pretty shitty 14.2
- The mid-range Cirrus Logic CL-GD-5422 with 1MB RAM (this is a decent card, know for compatibility but not necessarily speed): A barely bearable 24.7
- And finally, the "star" of the show, the Matrox: A whopping 10.9!
I said it was atrocious, didn't I? But hey, I'm gonna use this one with #OS2 anyway, so who cares about DOS performance, right? ;)
TL;DR: ISA Matrox cards are really, really slow in DOS.
I recently built an original Pentium 60MHz system, built on an ECS motherboard. Around the same time I received a "mystery" VGA card: A Matrox MGA Impression ISA card. And since most of my builds are "open builds" and therefore easily accessible, that machine got the pleasure of becoming the test bench for the Matrox.
As already revealed, the Matrox performs atrociously bad. So bad, in fact, that I had to test a couple other ISA cards to make sure it wasn't a system issue. I used my go-to benchmarking tool #3DBench from Phil's DOS Benchmark Pack. I really don't want to experience Doom with this card..
And without further ado, the contestants and their results in this spur-of-the-moment benchmark run:
- Baseline: A 32-bit PCI S3 Virge/DX based card with 4MB RAM: A perfectly workable 48.2
- The low-end Trident TVGA9000C with 512KB RAM (this is a real garbage card): A pretty shitty 14.2
- The mid-range Cirrus Logic CL-GD-5422 with 1MB RAM (this is a decent card, known for compatibility but not necessarily speed): A barely bearable 24.7
- And finally, the "star" of the show, the Matrox: A whopping 10.9!
I said it was atrocious, didn't I? But hey, I'm gonna use this one with #OS2 anyway, so who cares about DOS performance, right? ;)
See https://git.anduin.net/ltning/sshbench - I have not tested on anything slower than a crappy 486 (because no modern BSD will work on any of them) but EC ciphers generally come out on top every time - by a huge margin, too.
Also, testing hashtags on snac ;)
#OS2 #WarpServer #Memtest
The contenders: QuickView Pro version (dvpro), Digital Sound System 3.1 (dss) and MPXPlay 1.67 (mpx). The file: Astral Projection's "Bizarre Contact" from the album "Ten".
Enjoy these clips :D
I mean yeah, great, I get a proper BSD-4.4, 32-bit TCP/IP stack and tools. But it's taken me half a day. Getting the installation files over involved loading packet drivers and using #mTCP in a DOS session. Which works .. surprisingly well. But still .. FixPak43, reboot. MPTS, reboot. Netscape 2.02, reboot. Java 1.18, reboot. Feature Installer plug-in (no reboot). Then, finally, TCP/IP.
All this to have a machine to play with at #Blackvalley.
#OS2 #Retrocomputing #WhyAreYouReadingThis #GoDoSomethingUseful
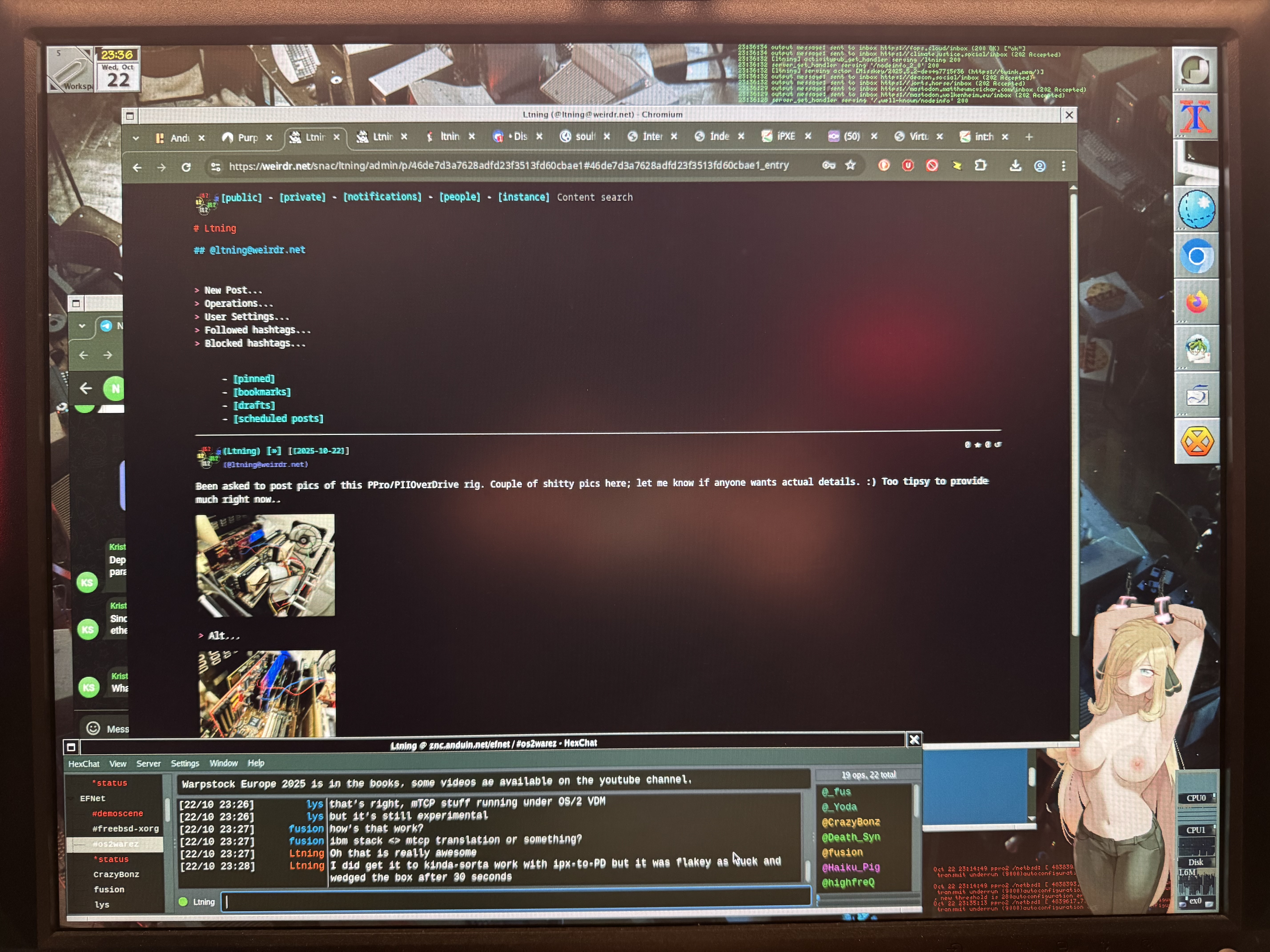
Only when a post is boosted or replied to do I run the risk of my hot-babe CPU monitor turning nsfw. So better keep it boring, I guess.
And if it wasn't for crypto being too slow to actually work I'd be doing the same on the 386SX-class machine that I also have running NetBSD. But with a hyper-optimized SSH handshake taking over a minute, I have no hopes for 2k RSA signatures or any kind of TLS handshakes with remote instances happening in anywhere near the timeframe they would need to..
![[?]](https://weirdr.net/snac/ltning/s/271784d3d55493d08c915e5bb7862aaf.jpeg)